Trust Centre
Security and compliance at CompleteFlow
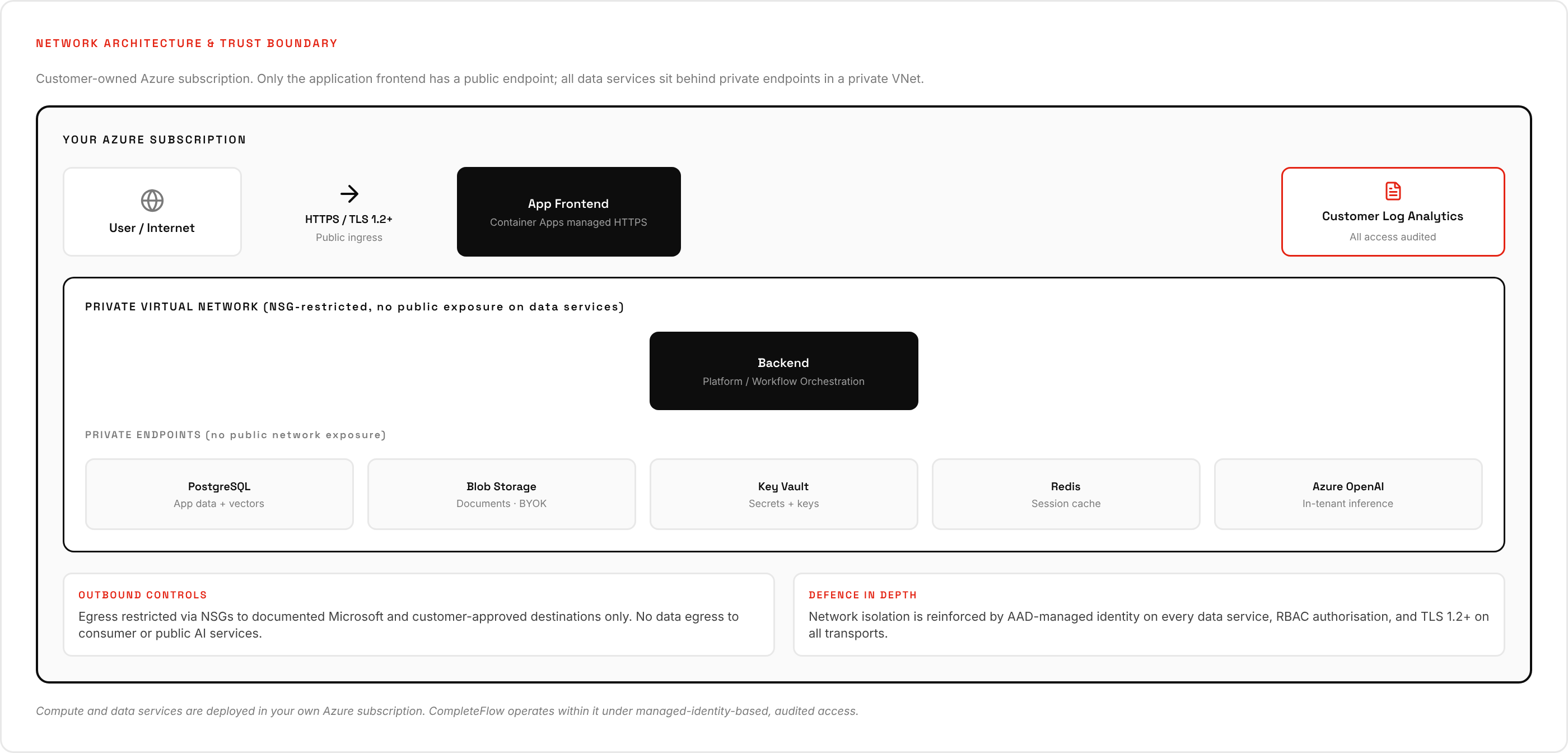
CompleteFlow is an enterprise agentic AI platform built for regulated sectors. Every customer is deployed into a dedicated Microsoft Azure subscription in the UK, under a control framework aligned with ISO/IEC 27001:2022 Annex A. This Trust Centre holds the live versions of our architecture, policies, and plans.
At a glance
Tenancy
Dedicated Azure subscription per customer. No shared compute, database, or storage between customers.
Data residency
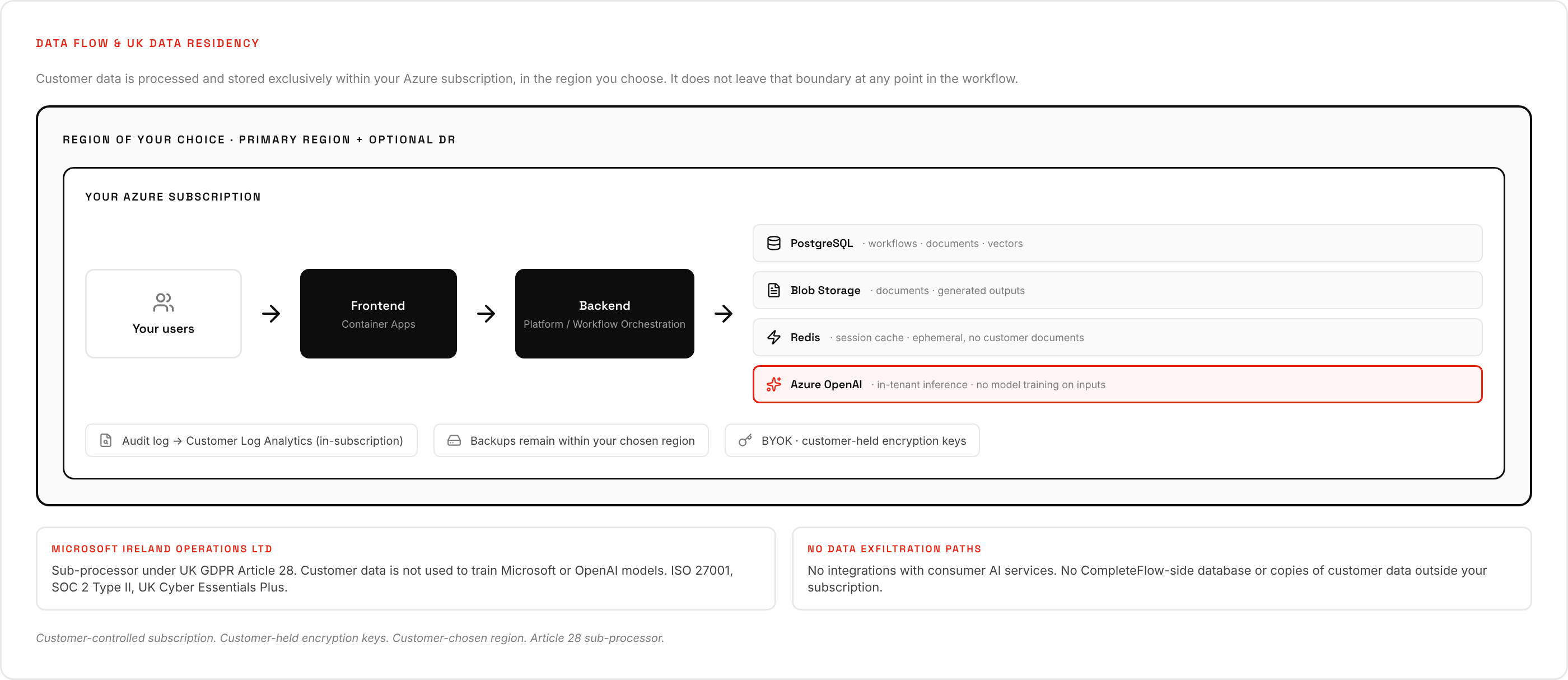
Azure UK South (London) by default; optional DR to UK West (Cardiff). Customer data does not leave the UK.
Encryption
AES-256 at rest, TLS 1.2+ in transit. Keys held in customer-controlled Azure Key Vault; BYOK supported.
AI model
Azure OpenAI Service in the customer tenancy. Inputs never used to train Microsoft or OpenAI models.
Overview
CompleteFlow Ltd is a UK-incorporated software provider. We deliver an enterprise agentic AI workflow automation platform to regulated mid-market firms in legal, insurance, and financial services. Because our customers operate under strict confidentiality, data protection, and sectoral regulatory duties, our platform and operating model have been designed for that audience from the outset.
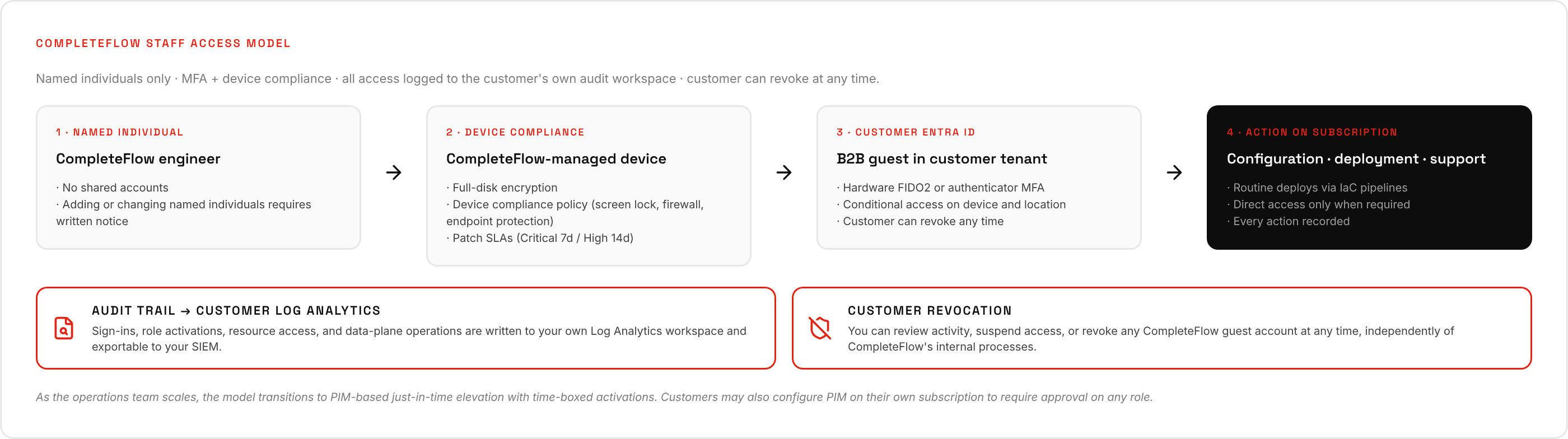
Our architecture is single-tenant in the strictest sense: each customer's deployment is a separate Microsoft Azure subscription, billed by Microsoft directly to the customer. CompleteFlow operates within that subscription under a managed services arrangement, using just-in-time access with documented approval and full audit trail. Customer data never leaves the customer's own Azure subscription; there is no central CompleteFlow-operated database or data lake into which customer content flows.
This Trust Centre is the authoritative collection of our security, data protection, and operational resilience documentation. The documents linked below are the live CompleteFlow policies and plans, reviewed annually (or on material change) and approved by the Director and Information Security Officer.
Documents
Each document carries an identifier (e.g. CF-POL-001), version, and owner. Internal sections reference each other using the convention CF-DOC-001 section 5.2.
Architecture and Security Overview
Platform architecture, network and data flow, cryptography, logging and monitoring, AI-specific controls, sub-processors, BCDR, and vulnerability management.
Information Security Policy
Master ISMS policy aligned with ISO/IEC 27001:2022 Annex A. Governance, roles, risk management, training, background checks, incident management, audit.
Data Protection Policy
UK GDPR compliance, lawful basis, data subject rights, international transfers, DPIA process, breach notification, ICO registration.
Access Control Policy
Authentication, authorisation, password standards, RBAC, privileged access management (PIM), joiner / mover / leaver process.
Acceptable Use Policy
Acceptable use of CompleteFlow devices, accounts, networks, and sanctioned software and AI tools. Prohibited activity and disciplinary consequences.
Data Retention and Disposal Policy
Retention schedule by data category, secure deletion procedures, deletion certificates, contract-termination data return.
Supplier Management Policy
Sub-processor selection, security due diligence, onboarding, ongoing monitoring, change notification, offboarding.
AI Governance and Acceptable Use Policy
Provider / deployer responsibilities, model selection, human oversight, prompt injection controls, personnel use of AI tools, prohibition of data leakage to public AI.
Secure Development Lifecycle Policy
Threat modelling, secure coding, code review, automated security testing, dependency and secret management, release gating, change control.
Incident Response Plan
Severity classification, response procedures, UK GDPR Article 33 alignment, support hours, post-incident review.
Business Continuity and Disaster Recovery Plan
Backup posture, cross-region failover, testing schedule, UK data residency. Recovery objectives agreed per customer SLA.
Risk Register (Summary)
Summary of the current CompleteFlow risk register: top risks, current controls, residual scoring, and direction of travel.
Architecture at a glance
How the controls in the policies above fit together. Full detail in CF-DOC-001.
Certifications and alignment
CompleteFlow inherits the certifications held by Microsoft Azure at the infrastructure layer and is actively preparing its own certifications at the CompleteFlow Ltd layer.
| Certification / registration | Entity | Status |
|---|---|---|
| ISO/IEC 27001 | Microsoft Azure (inherited) | Held |
| ISO/IEC 27017 | Microsoft Azure (inherited) | Held |
| ISO/IEC 27018 | Microsoft Azure (inherited) | Held |
| SOC 2 Type II | Microsoft Azure (inherited) | Held |
| UK Cyber Essentials Plus | Microsoft Azure (inherited) | Held |
| UK Cyber Essentials Plus | CompleteFlow Ltd | In preparation |
| ISO/IEC 27001:2022 | CompleteFlow Ltd | In preparation |
| ICO registration (controller + processor) | CompleteFlow Ltd | Held |
Current Microsoft attestations are published at the Microsoft Trust Center. CompleteFlow's ICO registration covers both controller and processor roles.
Reporting a security concern
If you believe you have found a security vulnerability affecting CompleteFlow or a CompleteFlow-operated service, please email security@completeflow.ai. We acknowledge reports during UK business hours and will follow up with a named point of contact.
Please do not test against live customer environments. Where a finding affects a specific customer deployment, we coordinate the response with the customer directly under our incident response process (CF-PLAN-001), including notification to the customer without undue delay.
Questions or requests?
Security contact: security@completeflow.ai. Privacy contact: privacy@completeflow.ai.
Contact CompleteFlow